Table of Contents
Introduction
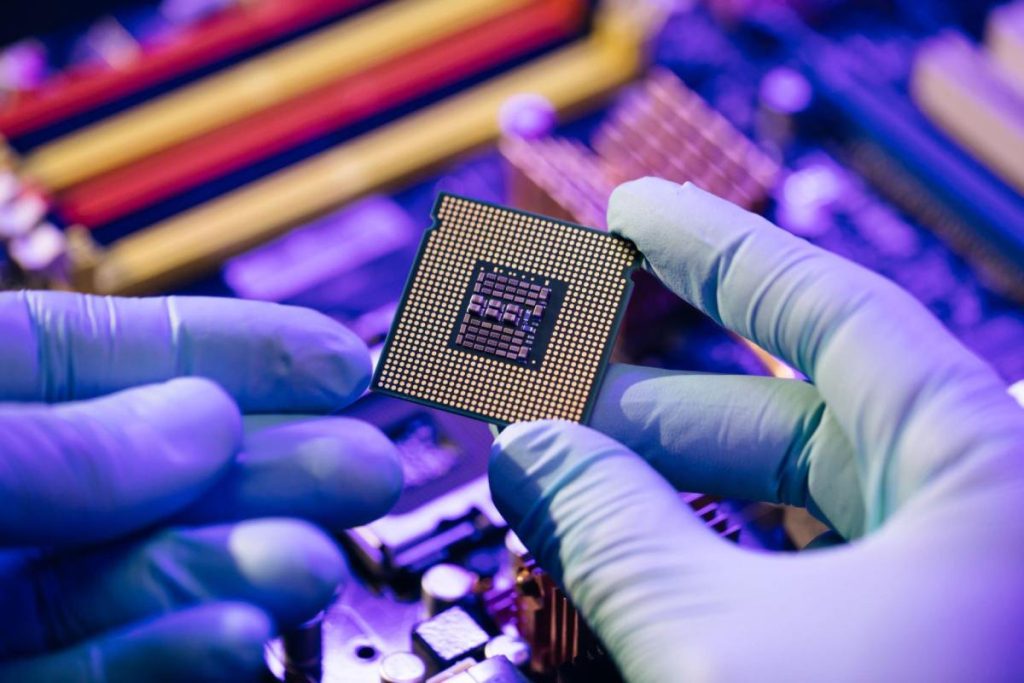
Secure Processor: Test and develop a new secure computer processor that misleads hackers by randomly changing its infrastructure, thus making it virtually impenetrable. Last summer, 525 security researchers spent three months trying to penetrate the Morpheus processor.
Others also tried, and all attempts failed. The study was part of a program sponsored by the u.s and the advanced defense research agency DARPA to design a secure processor capable of protecting vulnerable software.
A highly secure processor that misleads hackers by turning a computer into a puzzle – a fast processor capable of protecting vulnerable software. A secure processor that can defend any software it works on from the attack.
Processor: a piece of computer equipment capable of managing software. The processor is the basis of all software systems. So a secure processor can protect any software it works on from the attack.
The team at the University of Michigan developed the Morpheus processor, which misleads attacks by turning a computer into a puzzle, for the first time in 2019.
The processor has a standard ×86 for most laptops and ARM for most phones. The program’s set of instructions to run through the processor.
Processors also have micro-structures that allow for implementing the set of instructions. The speed of that implementation and how much energy they consume.
Hackers must be closely familiar with micro-structure to introduce malicious or harmful software into vulnerable software.
Therefore, not only do the attackers have to reflect the geometry of the microstructure. But they have to do so very quickly. Thanks to Morpheus, the pirate faces a computer he has never known before and will never see again.
The Importance Of Secure Processor
To make a security exploit, hackers use software vulnerabilities to access the device. On entry, they plant their malicious software designed to infect the host device to steal sensitive information or spy on users.
Repairing individual software vulnerabilities is the usual approach to computer security to prevent hackers from entering.
For these patch-based technologies to succeed, programmers must write perfect software without flaws.
But the idea of creating an ideal program is unrealistic, so if you ask any programmer, the flaws are everywhere. And finding security flaws is more difficult because they do not affect the normal process of the program.
The Morpheus takes a distinct security approach by strengthening the primary processor to prevent attackers from implanting malicious software into the device.
In this way, Morpheus protects any software through which it works.
Other Research Being Worked On Processor
Processor designers have long viewed security as a problem for computer system programmers since programmers have created software flaws that lead to security concerns.
But computer designers recently discovered that computer devices could help protect vulnerable software.
Academic Efforts, Such As Strengthening Instructions On The Capability Of Risc Equipment At Cambridge University. Have Shown Strong Protection Against Memory Defects. Business Efforts Have Also Begun, Such As Intel’s Soon-To-Be-Released Flow Control Application Technology.
Morpheus takes a markedly different approach to ignore flaws and instead makes its internal implementation random to thwart the exploitation of defects.
Fortunately, these are complementary methods. And collecting them will likely make it more challenging to penetrate systems.
What’s Next?
Consider how to apply the essential design aspects of Morelos to protect sensitive data in users’ devices and cloud services. In addition to randomly identifying the details of system implementation, how can we make data random in a way that preserves privacy while not burdening system programmers?
Conclusion
A secure processor is a computer-on-a-chip, or microprocessor, dedicated to performing cryptographic operations. It is embedded in multiple physical security measures that give it a degree of tamper resistance.
Also Read: How Many Seconds in a Day – Calculate Seconds in a Day